Multi-Device Command Deck
Plan changes across many devices. Lock the scope. Catch hallucinations before they reach the wire. Roll back if you need to. All from one deck.
Multi-device changes are where mistakes get expensive
Run the right command on the wrong device. Run a slightly-wrong command on the right device. Get a confident-sounding suggestion from a chatbot that hallucinates a flag. Any one of these can take down a campus VLAN at 2 a.m.
The Command Deck makes the safe path the easy path: agree on a scope, get a per-device plan, see exactly what AI inferred vs. what came from your verified library, then execute under guardrails that won't let the plan drift.
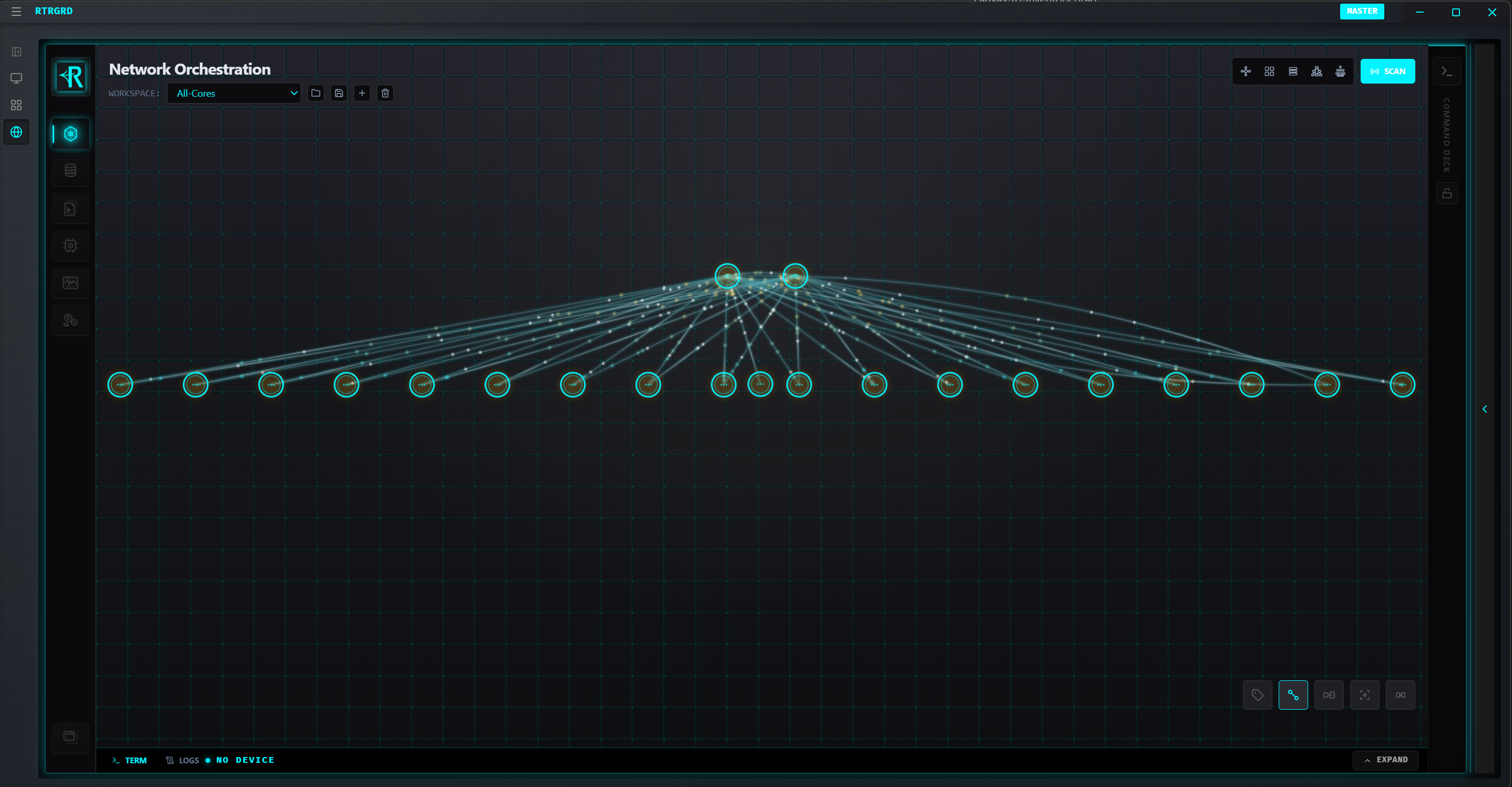
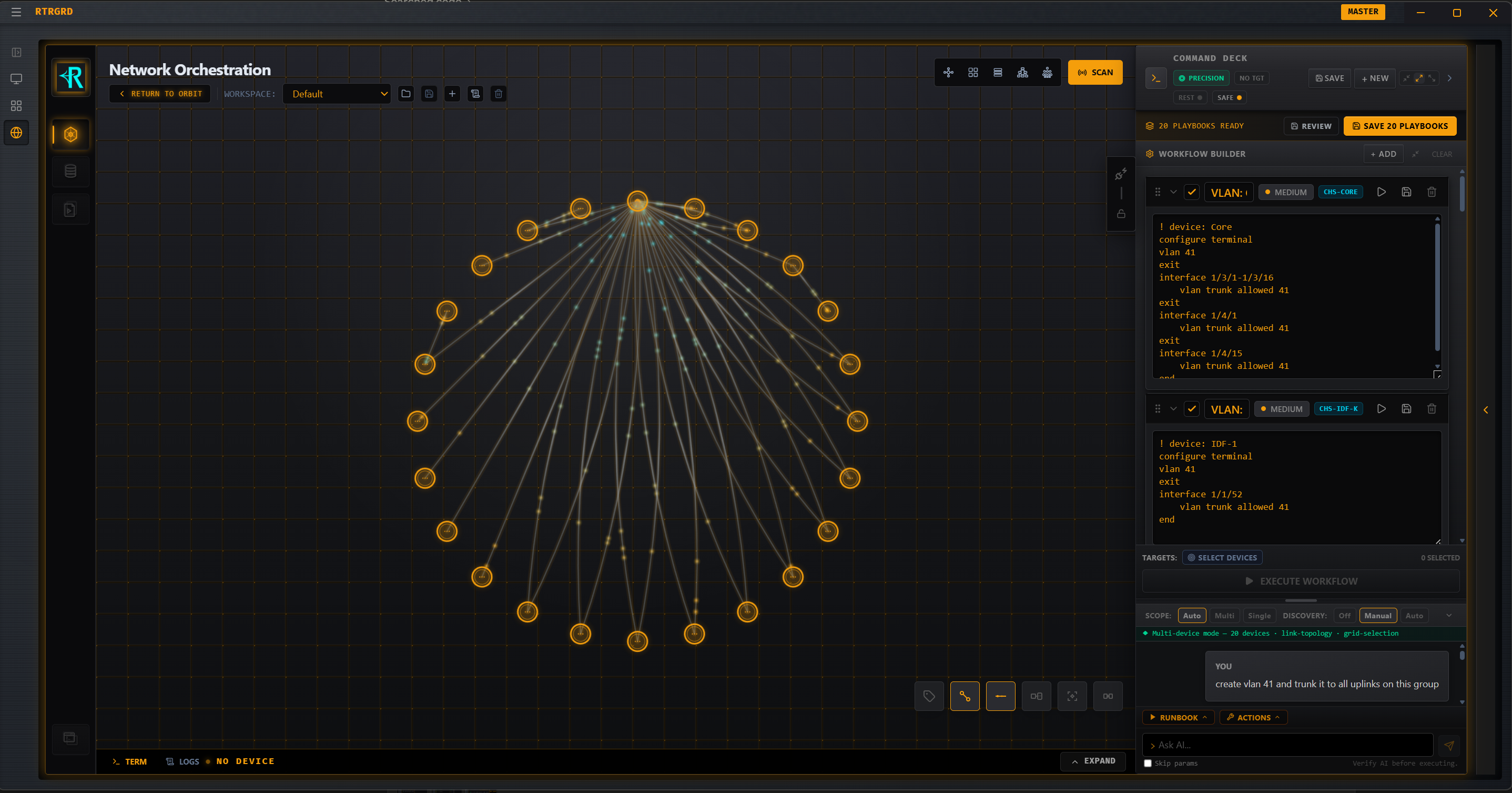
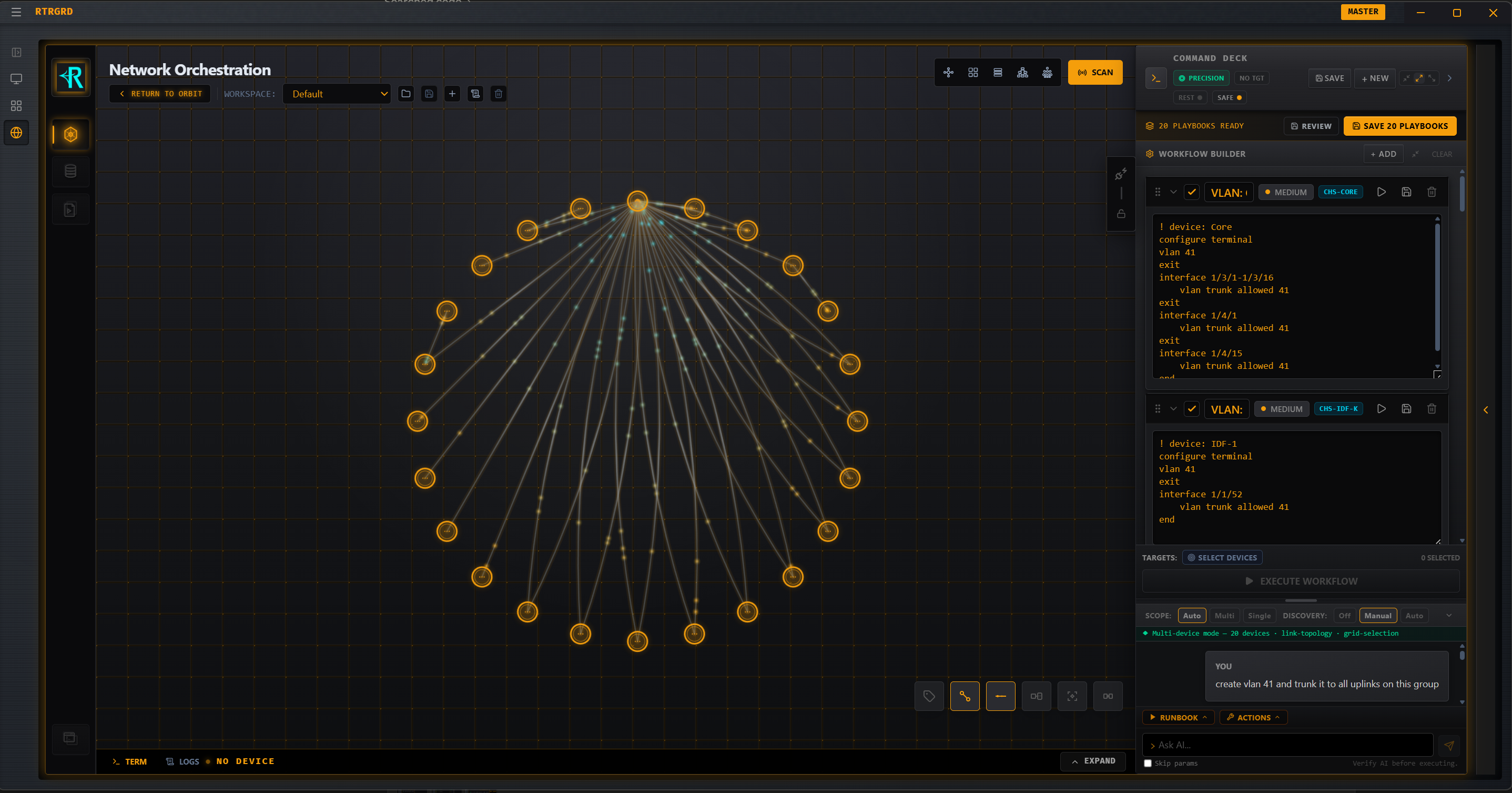
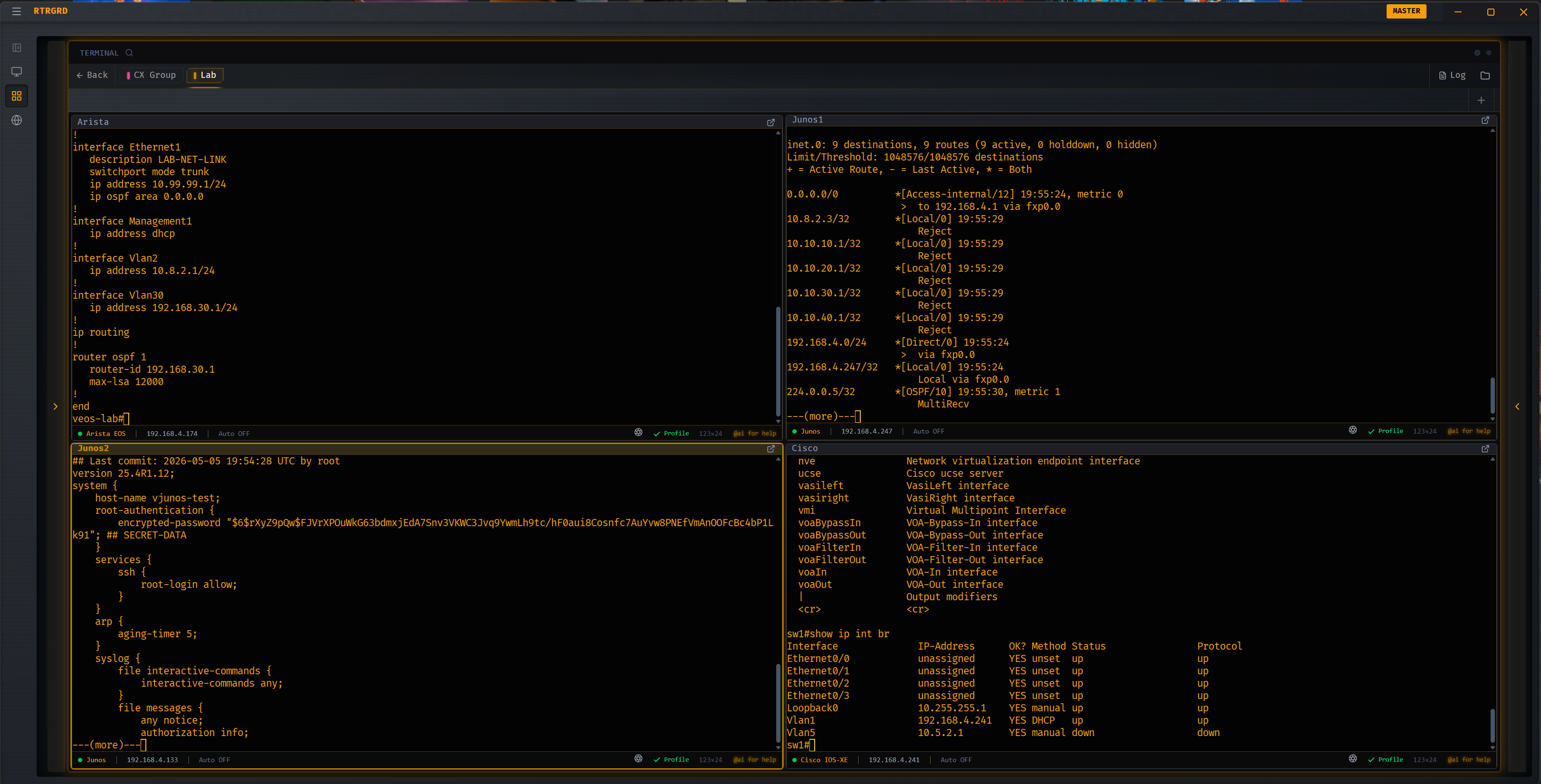
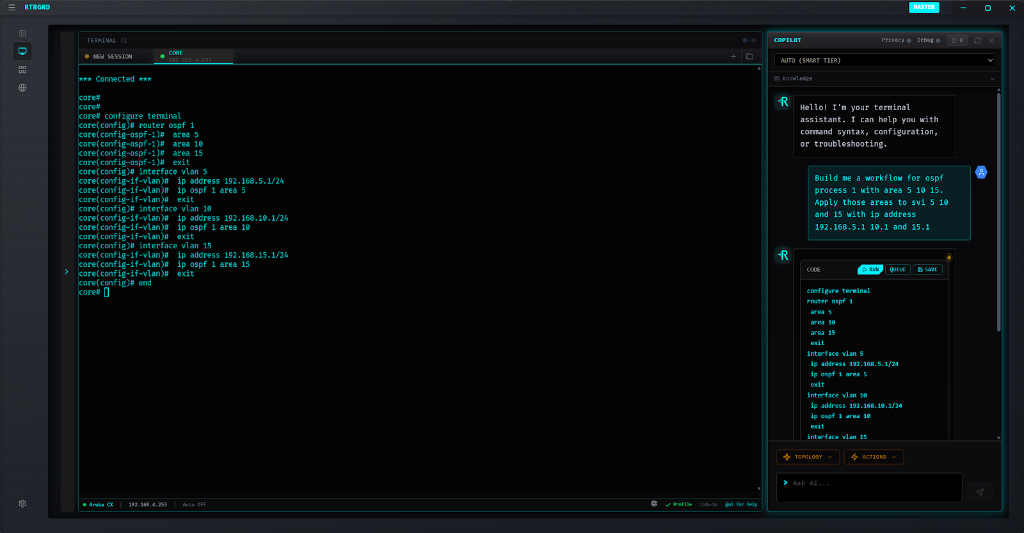
One plan, translated for every device
Describe the change once — "add VLAN 240 for guest Wi-Fi to the access layer" — and the Deck builds a per-device scaffold that already speaks the right CLI dialect for each target.
- translate OS-aware translation — Cisco IOS, Aruba CX, Junos, Arista EOS, NX-OS, FortiOS, PAN-OS each get their native syntax
- summarize ACTIONS_SUMMARY — Plain-English recap per device of what will change before any command runs
- view_column Side-by-side review — See all devices' scaffolds in one view; spot inconsistencies instantly
- history Persistent across sessions — Plans survive disconnects, tab closes, and machine restarts
A signed boundary the Deck won't let you cross
The biggest risk in a multi-device change is silent expansion of scope —
an extra interface, a stray no shutdown, a generated command that touches
something nobody agreed to. The SCOPE TOKEN is a cryptographic boundary issued when the plan
is approved. Any command that strays outside the token's declared targets is blocked.
- verified_user Targets locked — Token names exact device IDs; wrong device = rejected
- policy Surface locked — Token names which interfaces / VLAN IDs / route-maps are in scope; out-of-scope edits = rejected
- block AI can't override it — The validator runs after the model produces output; clever prompting can't bypass it
- receipt_long Audit-ready — Every rejected command is logged with the token, the proposal, and the reason
Edit a plan without losing the audit trail
Plans evolve mid-change-window. AMENDMENT MODE lets you re-open an executed plan, adjust the parts that need adjusting, and re-validate against the same guardrails — without losing the original record of what ran when.
- difference Clean diff — See only what changed since the last approved version
- check_circle Re-validation required — Every amendment goes through SCOPE TOKEN and syntax checks before it can run
- timeline Append-only history — Original plan, every amendment, and every execution kept in order
- undo Rollback per device — Combine with checkpoint safety to back out a single device without unwinding the whole change
Every AI-generated command is labeled
When the model fills a gap your verified library couldn't, the Deck marks the result so you know it. Confident-sounding output isn't the same as grounded output, and the UI never lets you forget which is which.
| Prefix | Meaning | Grounding |
|---|---|---|
VERIFIED |
Pulled from your local 30,000+ command corpus | Vendor docs + RAG match |
AI BEST-GUESS |
Synthesized by the model, labeled and gated | No verified match — review required |
USER-EDITED |
Hand-modified by you | Original source preserved alongside |
- percent Confidence score per command — Surfaced inline; below a threshold, the Deck warns before letting you queue it
- menu_book Citation chip — Click to see the exact RAG document or vendor page the suggestion was grounded in
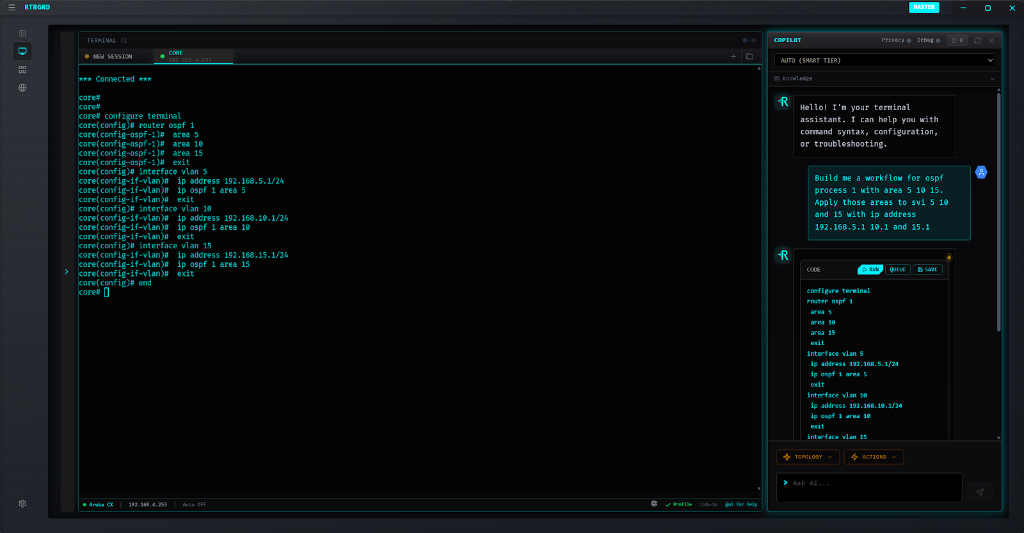
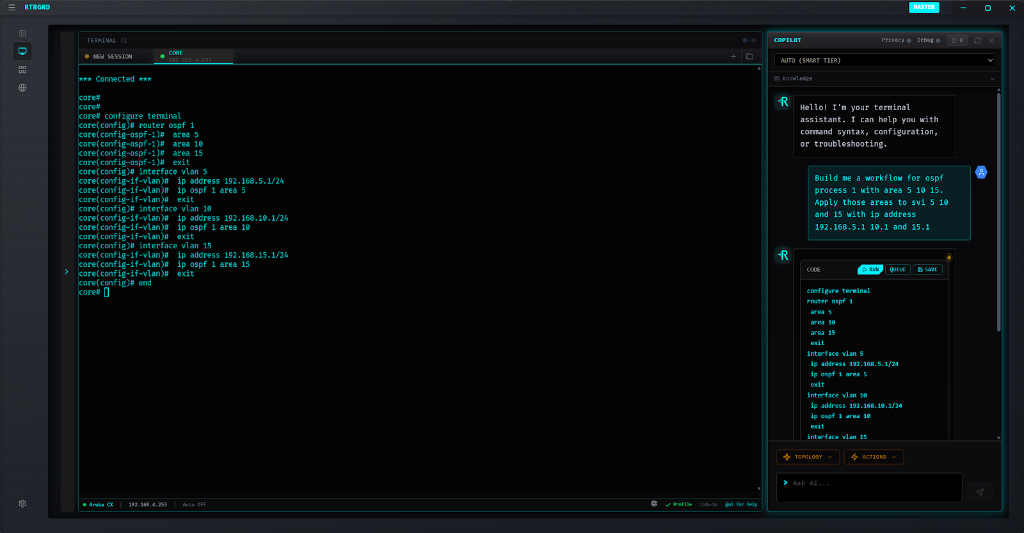
The validator knows what your device actually accepts
Generic chat models will happily produce a Cisco-flavored command for an Aruba box. The Deck won't let it ship. Each per-device scaffold is checked against the device's real grammar — drawn from the same verified library that powers Ghost Text and Copilot — before it's eligible to execute.
- fact_check Pre-flight grammar check — Unknown keywords, wrong argument order, missing required arguments — all surfaced before commit
- checklist Vendor-aware — Cisco IOS / IOS-XR / NX-OS, Aruba CX / AOS-S, Junos, Arista EOS, Palo Alto, Fortinet, F5, Linux all handled independently
- close Hallucination block — Commands the model invented but that the device's grammar doesn't recognize are filtered out, not "best-effort run"
Use your own provider for the AI lift
Apex subscribers can plug in their own Gemini, OpenAI, Anthropic, xAI, or Groq API keys. The Deck still applies the same SCOPE TOKEN, sanitization, and grammar validation — but the inference call goes directly to your account, not RTRGRD's. You pay the provider, you keep the audit trail, you set the data-retention rules.
20+ OS Types Supported
Plan a multi-device change without holding your breath
Multi-Device Command Deck ships with RTRGRD-Apex. 30-day full-access trial. No credit card required.
arrow_forward See Apex Pricing